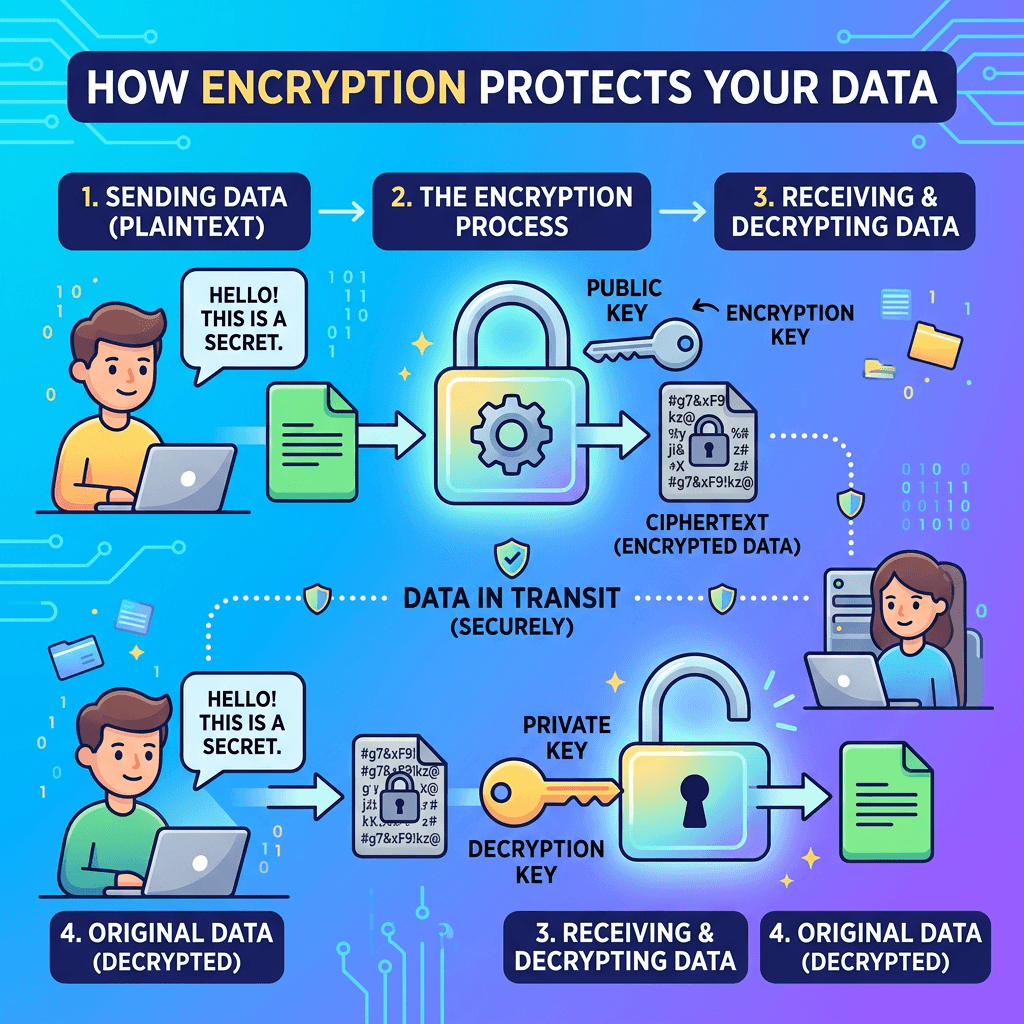
What Is Encryption and Why It Keeps Data Safe
Encryption scrambles data so only trusted eyes can read it
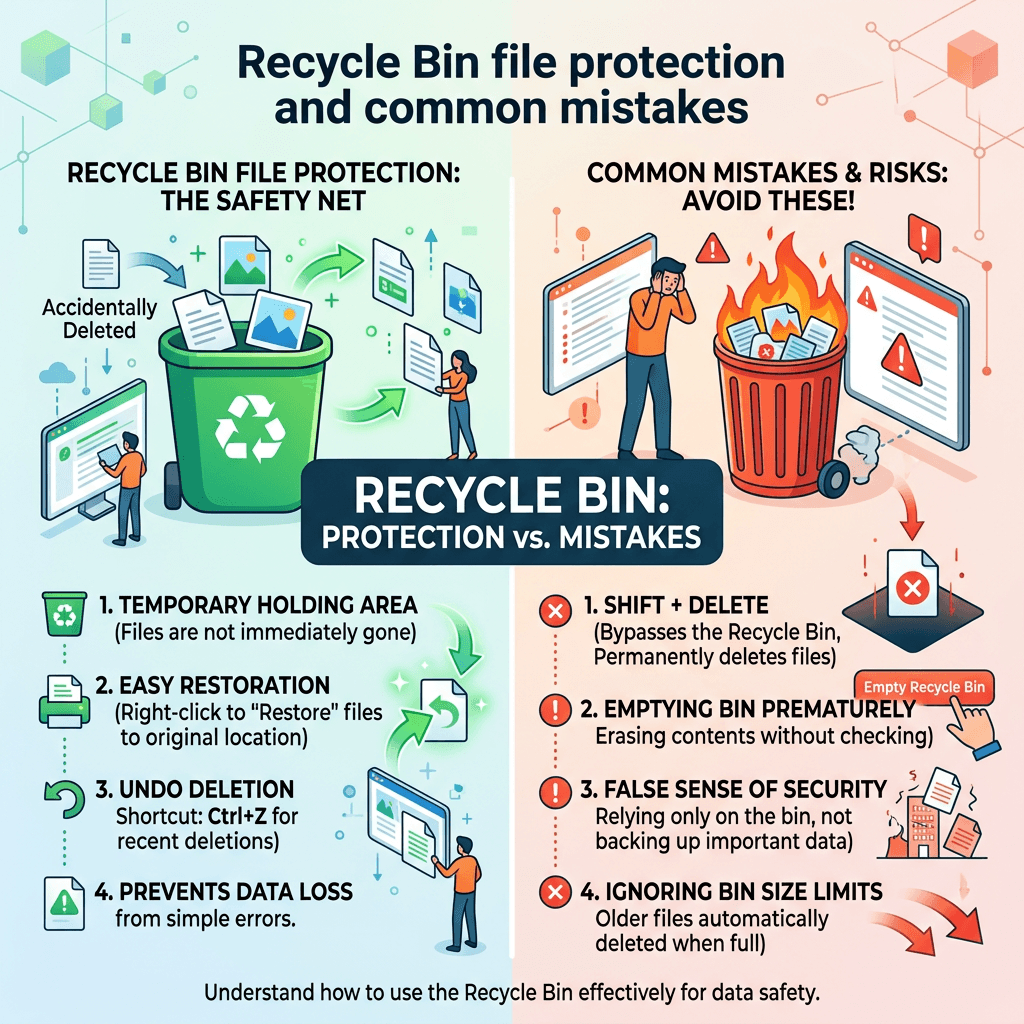
What Is the Recycle Bin Beginners Guide to Safer Files
Learn how the Recycle Bin protects deleted files
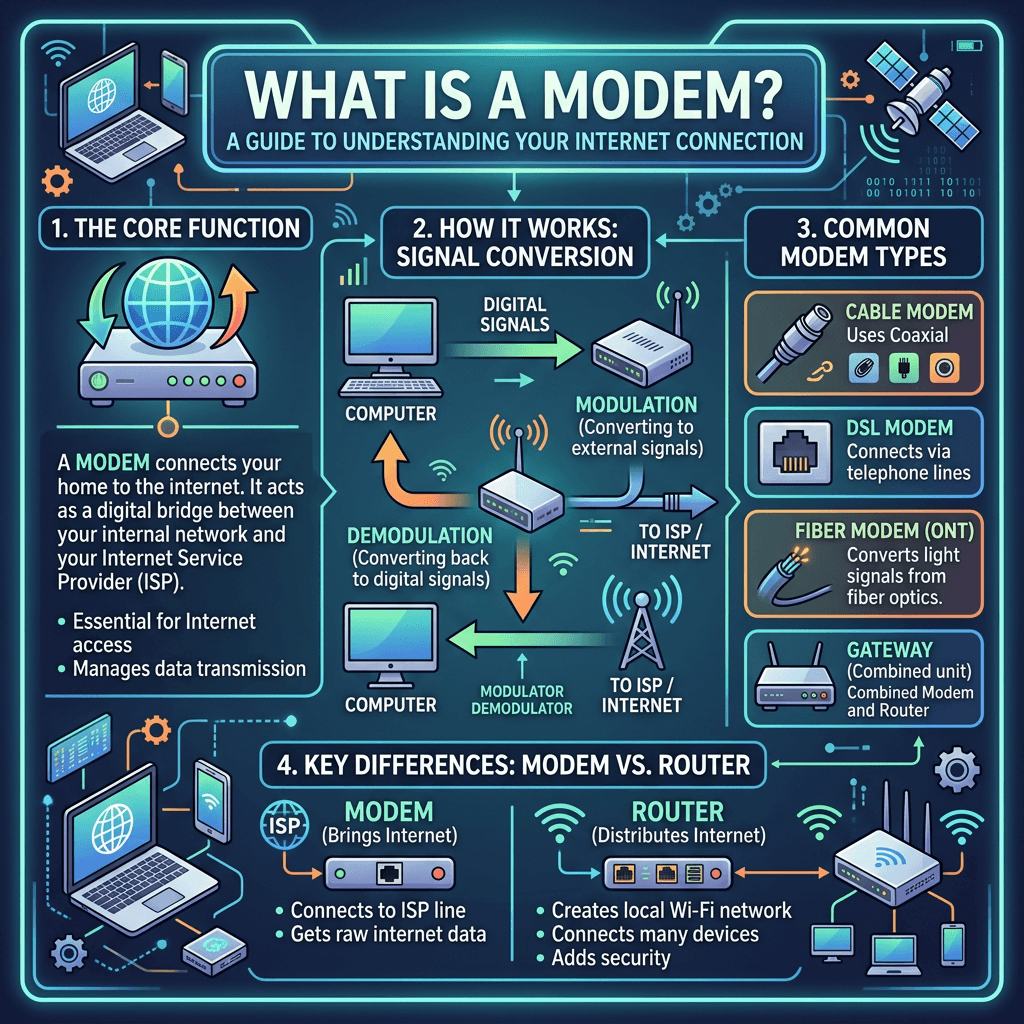
What Is a Modem Guide Learn How It Powers Your Internet
Discover how a modem connects your world online
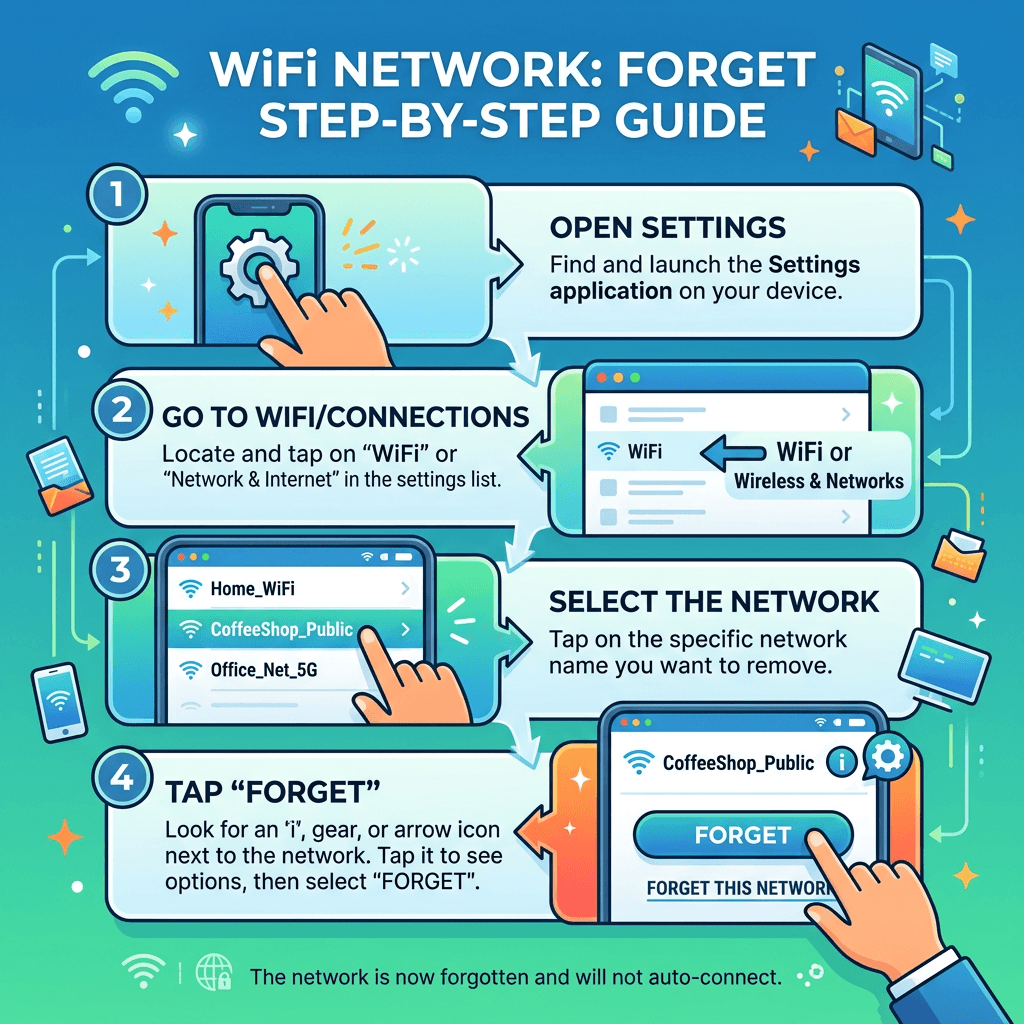
How to Forget a WiFi Network Fast A Simple Step by Step Guide
Quick steps to remove old WiFi networks easily
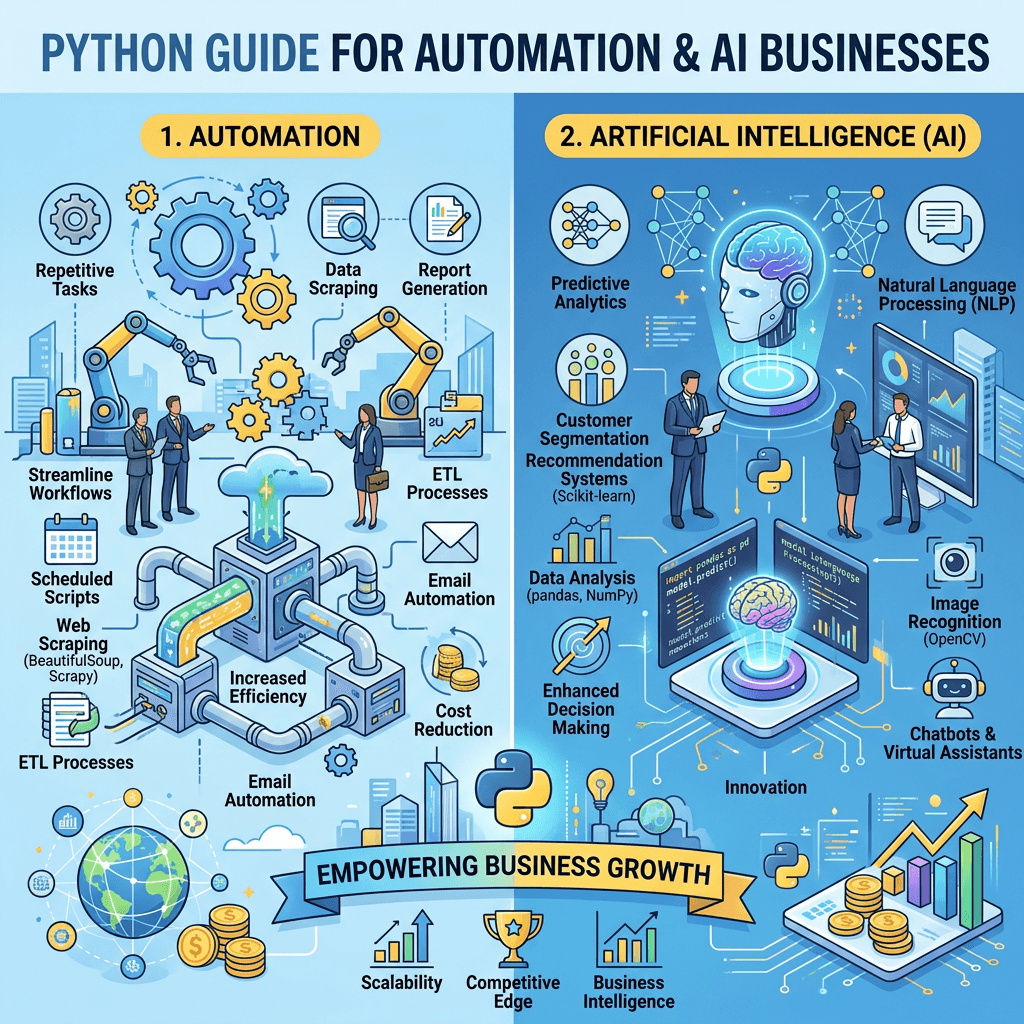
Python Guide What It Is and How It Powers Modern IT
Discover how Python powers innovation in modern IT
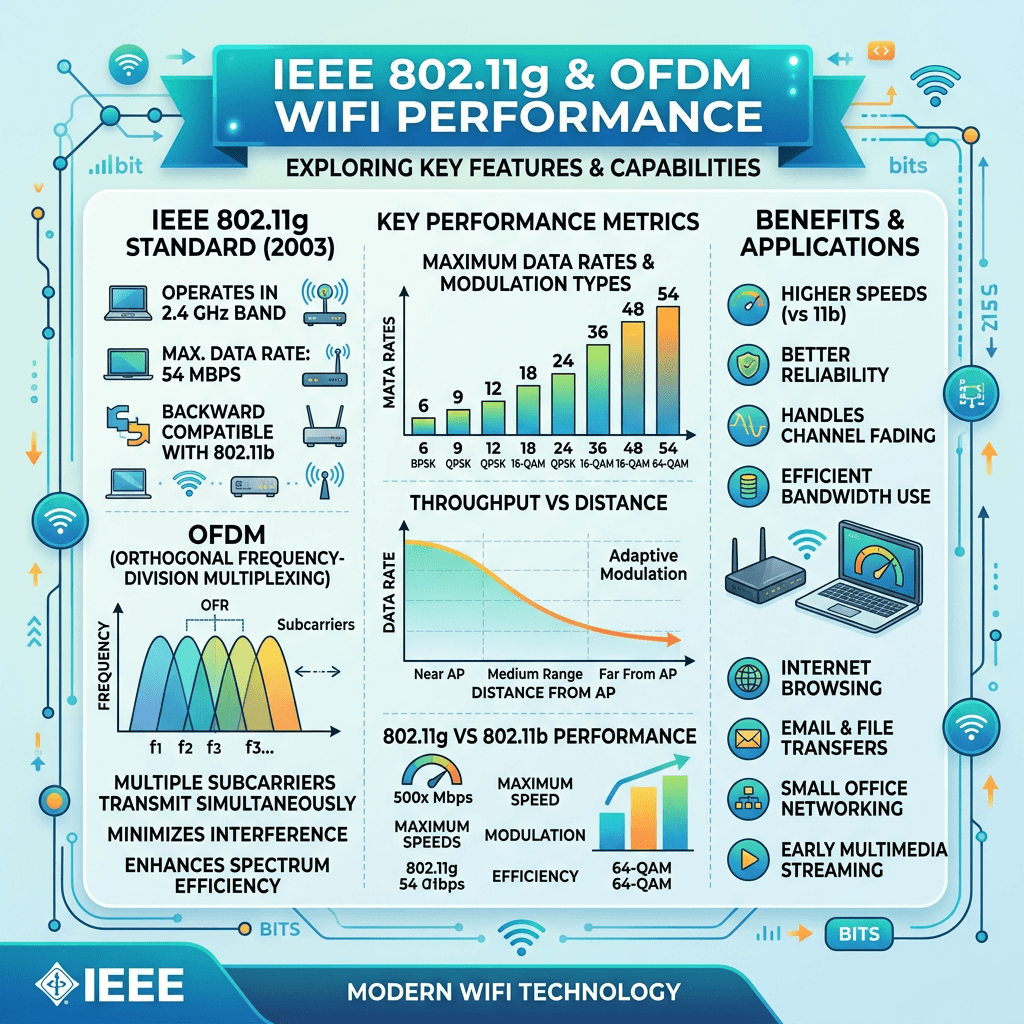
IEEE 802.11g Modulation Guide for Faster WiFi Performance
Understanding IEEE 802.11g modulation for faster WiFi
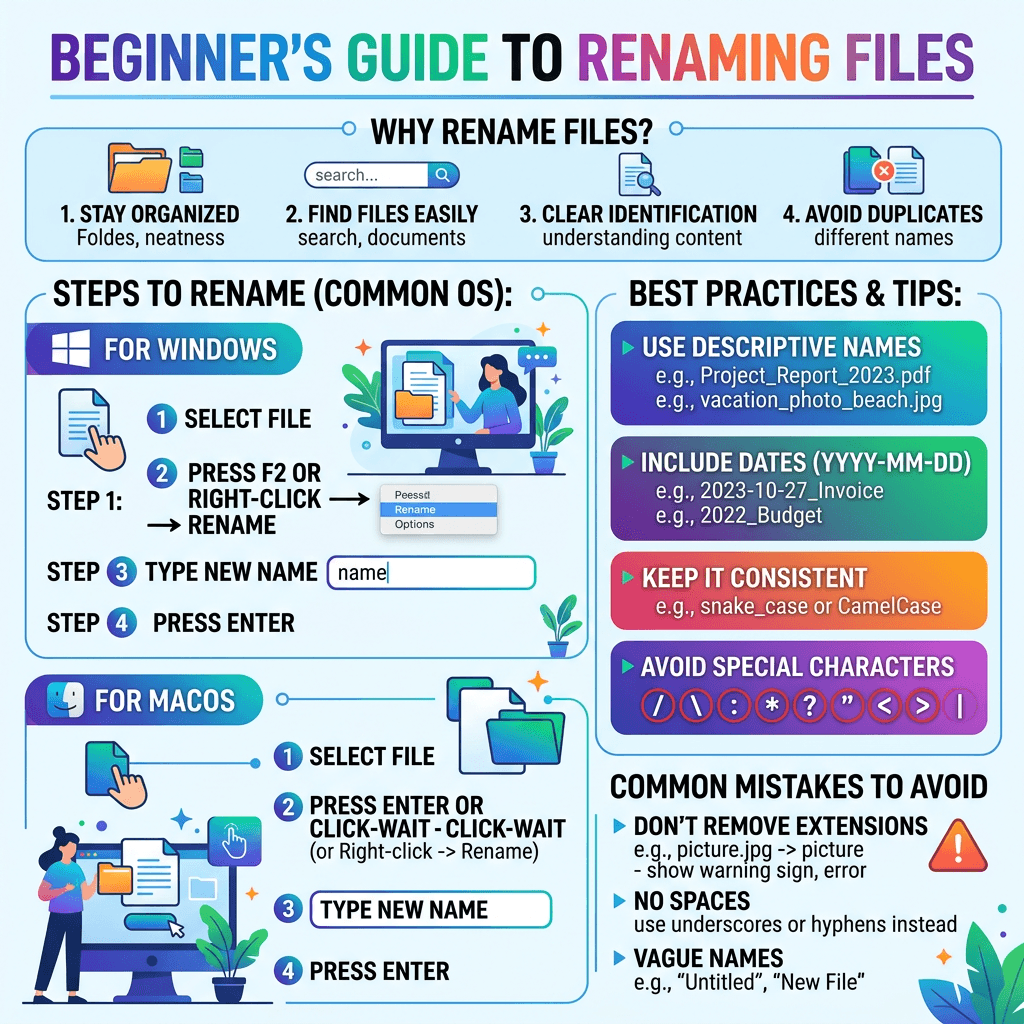
How to Rename Files Easily A Complete Beginner Guide
Learn to rename files fast with simple step-by-step tips
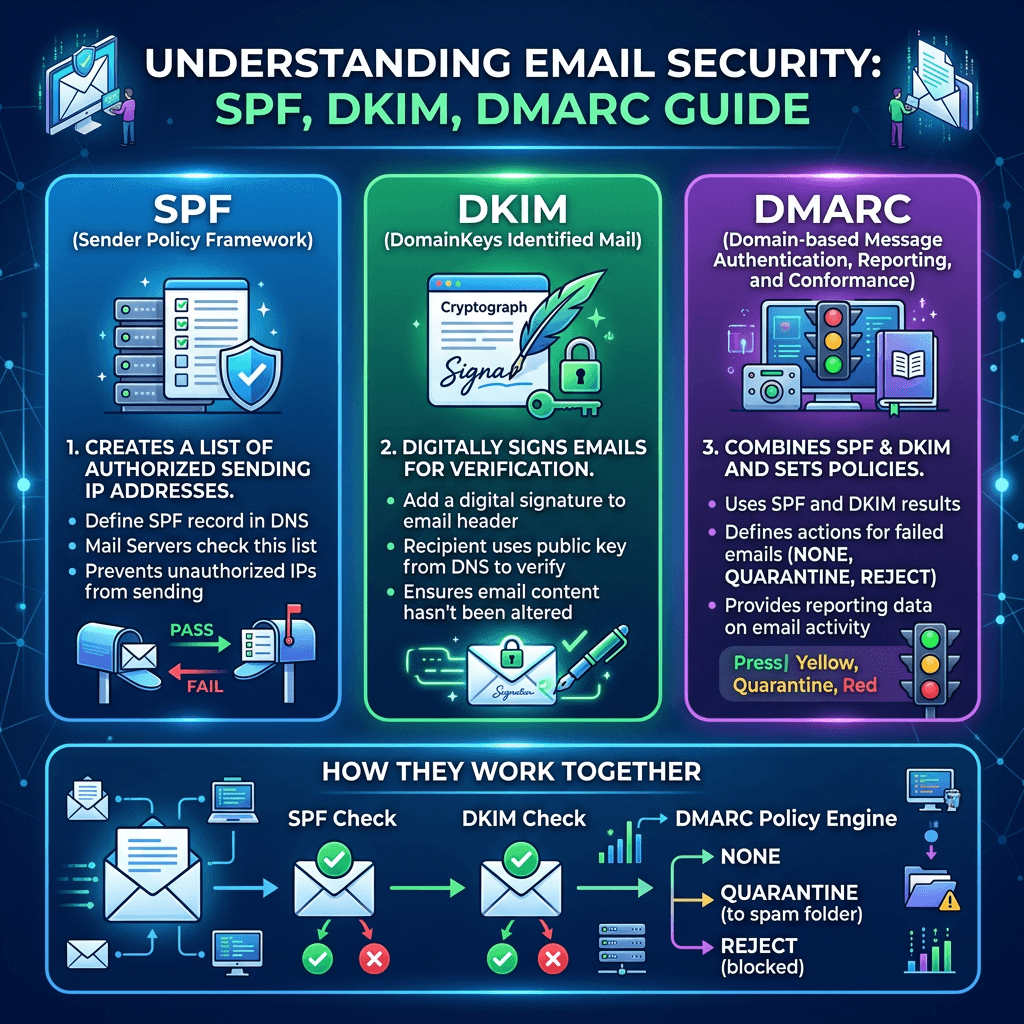
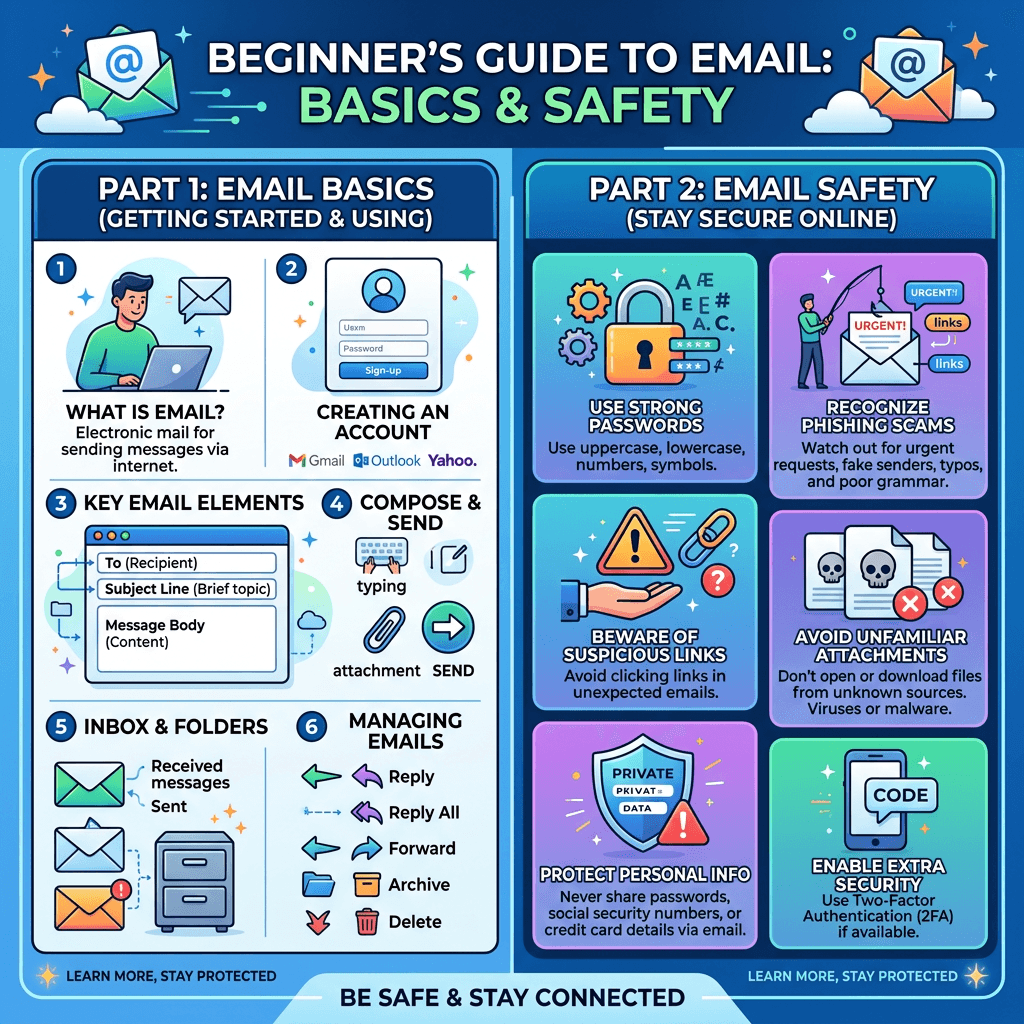
SPF DKIM DMARC Setup Guide for Secure Email Hosting
Protect your domain and boost email security today

Malware Guide What It Is and How to Protect Your Devices
Understand malware threats and protect your devices today
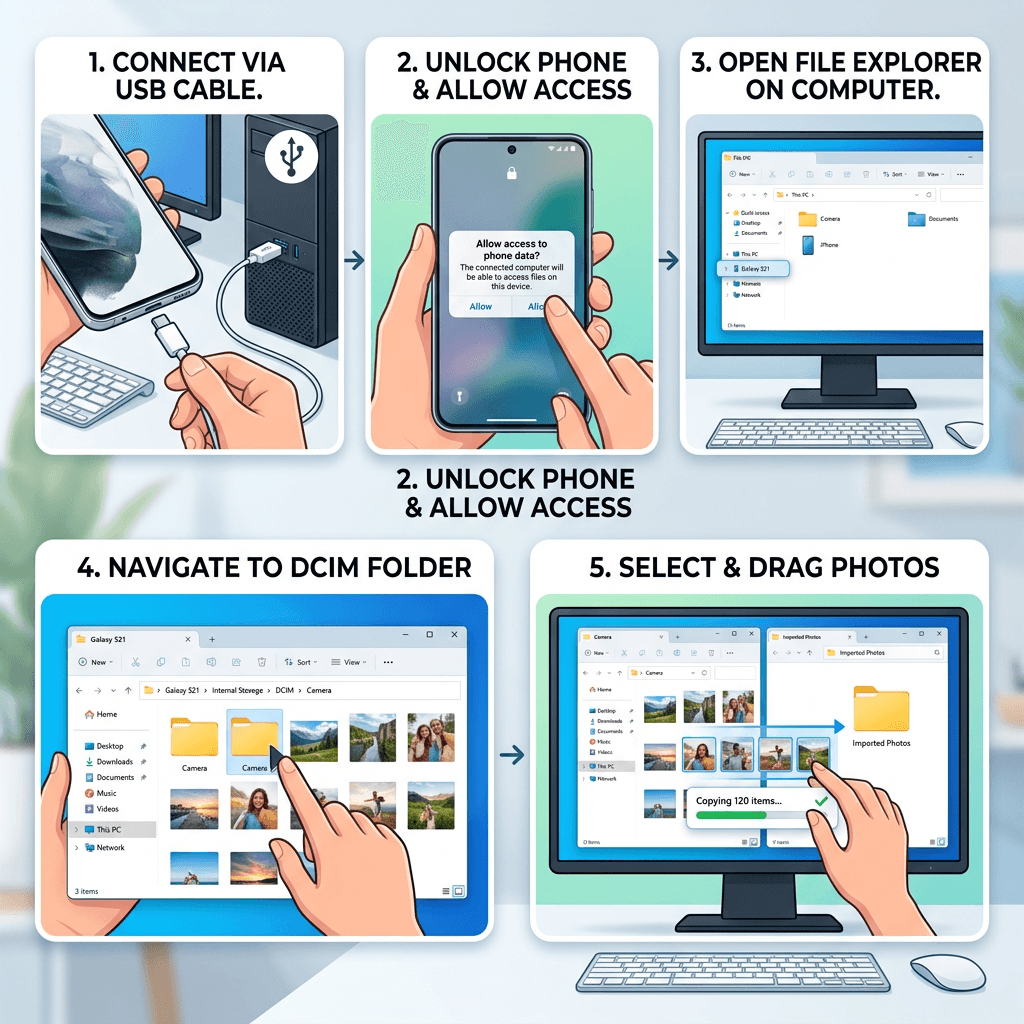
How to Transfer Photos to Computer Easy Smartphone Guide
Easily move phone photos to computer in minutes
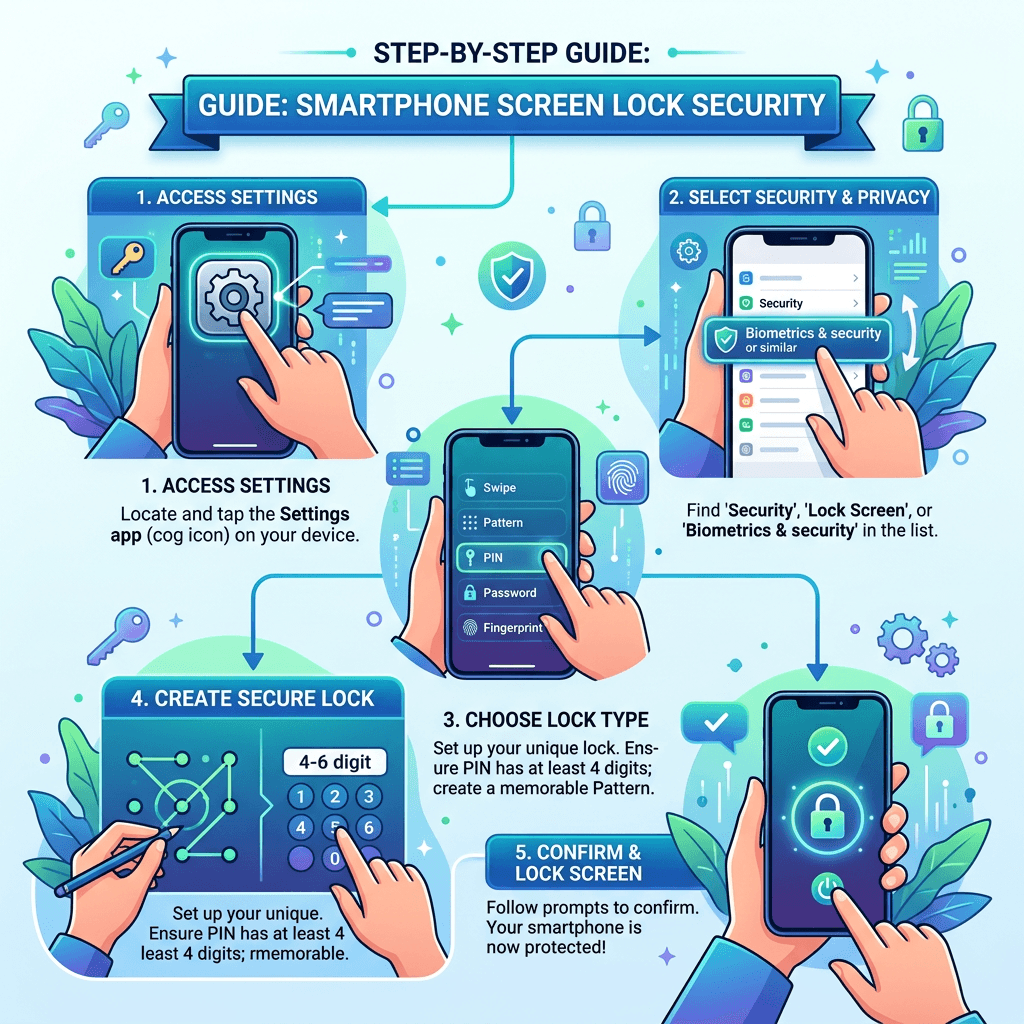
Smartphone Screen Lock Guide for Better Security
Protect your phone and data with easy screen lock steps
Google Chrome Guide What It Is and Why You Should Use It
Discover how Google Chrome simplifies your online world

SEO Guide for Beginners How to Boost Website Traffic Fast
Learn how SEO works and start boosting your traffic fast
How to Take a Screenshot Guide for Complete Beginners
Learn simple ways to capture your screen like a pro

Google Chrome Guide What It Is and Why You Should Use It
Discover why Google Chrome is the browser you need
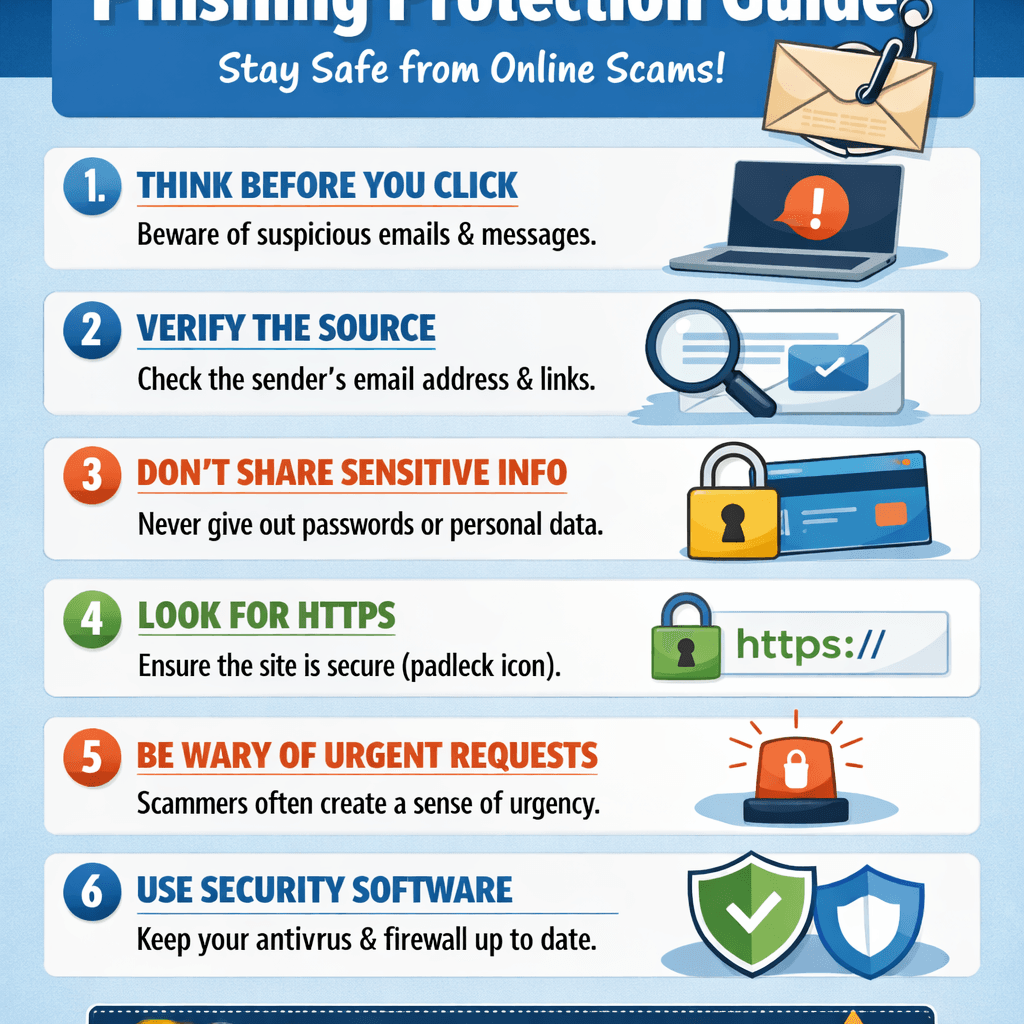
Phishing Guide How to Spot and Stop Online Scams Fast
Learn what phishing is and how to protect your data