
Entendiendo el cifrado WPA: TKIP vs. AES
WPA utiliza el cifrado TKIP y WPA2 puede emplear AES. TKIP fue creado para mejorar la seguridad del WEP, mientras que AES ofrece un nivel[…]

Examples of the WI-FI devices
These examples represent common hardware components and devices that conform to standard Wi-Fi specifications, facilitating wireless communication across diverse environments.

The maximum length of an Ethernet cable?
The maximum length of an Ethernet cable depends on the type of cable and the network specifications. For standard twisted-pair Ethernet cables, such as Cat5e[…]

Understanding OFDM and MIMO in Wireless Communication
OFDM (Orthogonal Frequency Division Multiplexing) is a digital modulation technique that improves data transmission over various channels by splitting streams into sub-streams sent over different[…]

The Birth of Wi-Fi: A 1997 Milestone in Wireless Networking
Wi-Fi was created in 1997 when the Institute of Electrical and Electronics Engineers (IEEE) established the 802.11 standards for wireless networking, which laid the foundation[…]

Sharing Content Legally: Tips for Website Owners
You can share content offers on other websites if you have the rights to do so. Key considerations include ensuring copyright compliance, providing proper attribution,[…]
Key Requirements for a Successful MVP
An effective Minimum Viable Product (MVP) requires core functionality focused on solving user problems, user-centric design for ease of use, a feedback mechanism for insights,[…]
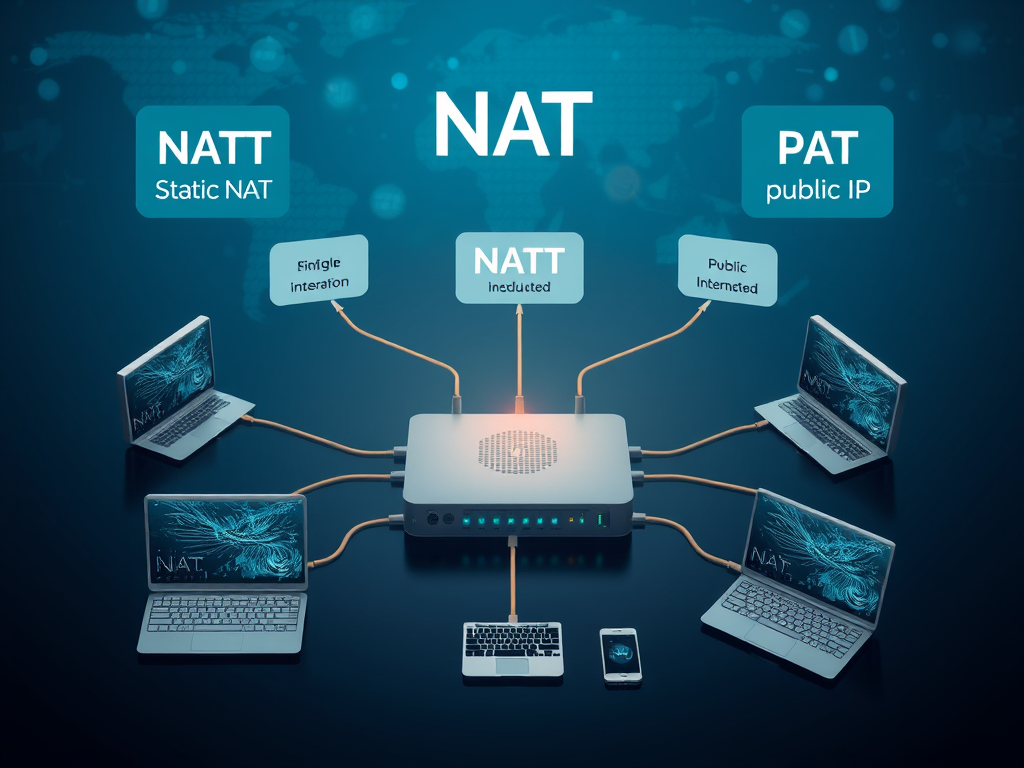
Understanding Network Address Translation (NAT)
NAT, or Network Address Translation, allows multiple devices on a local network to share a single public IP address, conserving IP addresses and enhancing security.[…]

Signs Your Computer Needs an Upgrade
Signs that your computer may require an upgrade include slow performance, frequent crashes, software incompatibility, insufficient RAM, outdated hardware, overheating, limited storage space, graphical issues,[…]

Benefits of Multi-Language IT Support
Having multi-language IT support can be beneficial depending on your organization’s needs. Here are a few reasons to consider: Evaluating the demographics of your users[…]

Choosing the Right Web Hosting: Key Factors to Consider
Choosing the right hosting for your website requires careful consideration of several factors. First, determine the type of hosting that suits your needs: shared, VPS,[…]
Should You Hire SEO Professionals?
Determining whether to engage professionals for search engine optimization (SEO) depends on several factors related to the scope and complexity of your website, as well[…]

Get Your Website Hosted from Just $1 a Month!
You can host your website for an incredibly low price starting at just $1 per month. This affordable option makes it accessible for individuals and[…]

Can Your Wi-Fi Be Accessed Remotely? Essential Tips
Wi-Fi networks can be accessed remotely under specific conditions, mainly due to poor security settings, such as weak passwords or outdated encryption methods. Additionally, routers[…]

How to Protect Your Wi-Fi: Top Security Measures
To secure your Wi-Fi network, change the default password, enable WPA3 or WPA2 encryption, disable SSID broadcasting, and implement MAC address filtering. Limit DHCP leases,[…]
Can I use a VPN on my home network?
Yes, using a VPN on your home network is possible by setting it up directly on your router, which ensures that all devices connected to[…]

Understanding Different Types of Internet Service Providers
There are various types of Internet Service Providers (ISPs) tailored to different user needs. Dial-Up ISPs connect via telephone lines, providing slower speeds for light[…]

Essential IT Functionality for Organizations
To identify necessary IT functionalities, focus on several key areas: infrastructure management (servers, storage, networking), security (firewalls, antivirus, encryption), software development (IDEs, version control), support[…]

Understanding Wi-Fi Technology and Its Key Components
Wi-Fi technology enables wireless communication over a local area network (LAN). Here’s a breakdown of how Wi-Fi works and its key components: What is Wi-Fi?[…]

Understanding Shared, VPS, Dedicated, and Cloud Hosting
The content compares four types of web hosting: shared, VPS, dedicated, and cloud. Shared hosting is cost-effective and beginner-friendly but offers limited resources and security.[…]

Understanding LAN, WAN, MAN, PAN, and VPN Networks
This content outlines the advantages and disadvantages of five different network types: LAN, WAN, MAN, PAN, and VPN. LANs provide high speeds and cost-effectiveness but[…]

Key Elements of a Wi-Fi Network Explained
A Wi-Fi network consists of several key elements: an Access Point (AP) creates a wireless local area network (WLAN) for device connectivity, while a router[…]

Understanding UHF Transmission Wavelengths
Ultra high-frequency (UHF) transmission operates within a wavelength range of about 1 meter to 10 centimeters, corresponding to frequencies from 300 MHz to 3 GHz.[…]

Enhancing Website Navigation for Better User Experience
The user experience on a website heavily depends on how easily visitors can find important information. Key factors include clear navigation with structured menus and[…]

Top Strategies to Build Your Email List Successfully
Building an email list is essential for online businesses and content creators. Effective strategies include creating valuable content like eBooks and engaging blog posts, promoting[…]