
Applications of VHF: TV, FM Radio, and More
The very high-frequency (VHF) transmission range, which extends from 30 MHz to 300 MHz, is utilized in various applications, including television broadcasts, FM radio, and[…]
Ventajas de las Topologías WiFi
La topología de red WiFi se refiere a la disposición de dispositivos en una red inalámbrica. Las principales son: estrella, malla, anillo y bus. Cada[…]
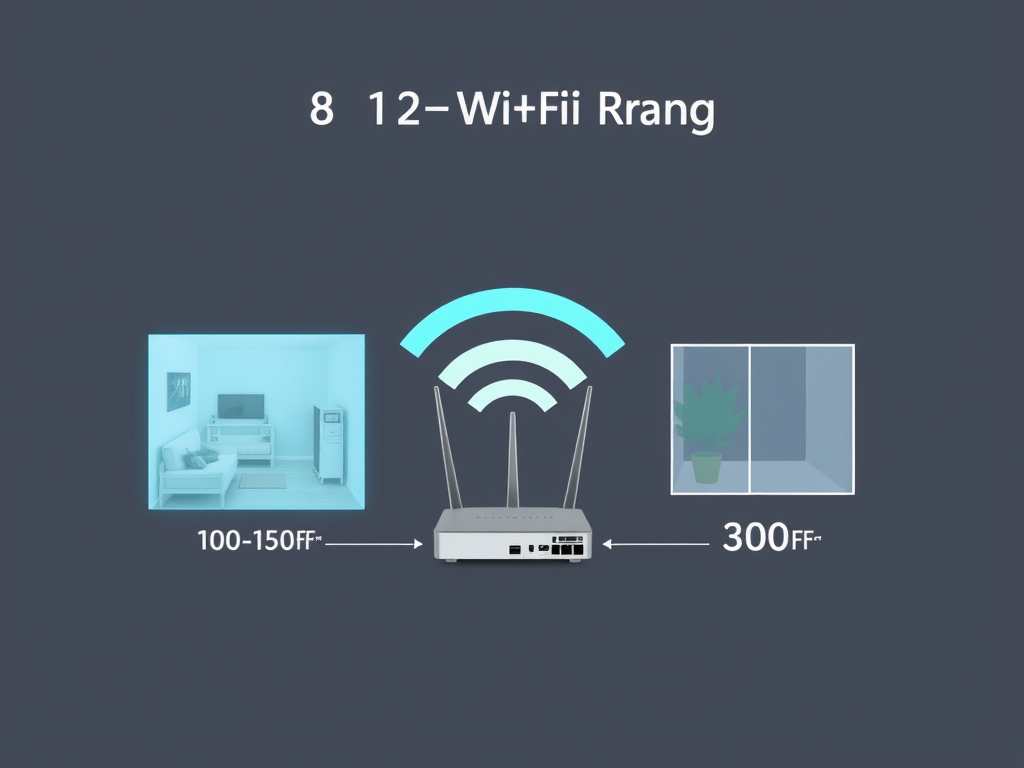
Understanding 802.11b Range: Key Insights
The range of the 802.11b standard is typically about 100 to 150 feet (30 to 45 meters) indoors and can extend up to 300 feet[…]

Essential Website Maintenance Tips for Optimal Performance
Regular site maintenance is crucial for optimal performance and user experience. Key aspects include uptime monitoring to ensure accessibility, analyzing page load speed across devices,[…]

Tipos de Topologías de Red WiFi: Una Guía Completa
La topología de red WiFi abarca la disposición física y lógica de dispositivos conectados. Incluye la topología en estrella, donde todos los dispositivos se conectan[…]

Guide to Building an Efficient Network for Your New Office
To set up an efficient, secure, and scalable network for a new office, choose a reliable ISP and connection type. Invest in high-performance routers, switches,[…]

Why You Should Use Multiple Locations for Data Backup
Storing backups in multiple locations offers several advantages. It enhances disaster recovery by safeguarding data against local catastrophes like fires or floods. Redundancy ensures data[…]
How Long Can You Register a Web Domain?
Web domains are registered for one to ten years, depending on the registrar and the top-level domain (TLD). Once the initial registration expires, owners can[…]

What is an SSID and Why It Matters for Your Wi-Fi Network
The Service Set Identifier (SSID) is a unique name used by wireless networks to identify themselves. It serves as a means for users to select[…]

Understanding WiMAX Throughput: Key Factors and Metrics
The throughput of the IEEE standard 802.16d, known as WiMAX, can fluctuate based on factors like network configuration, signal quality, and user density. In ideal[…]

Understanding Wi-Fi Standards: A Complete Guide
Wi-Fi technology operates on standards defined by the IEEE 802.11 family, supporting wireless local area networks (WLANs). The key standards include 802.11a (5 GHz, 54[…]
What do I do if my computer don’t work after a recent software update?
If your computer malfunctions after a software update, several troubleshooting steps can help. First, restart your computer to clear temporary glitches. Next, check for any[…]

Top 10 HTML Best Practices for SEO
To optimize your HTML code for search engines, follow essential practices such as using semantic HTML5 elements like

Risks of Wi-Fi: What You Need to Know
Wi-Fi technology enhances connectivity but poses several risks. These include security vulnerabilities leading to data breaches, privacy concerns through user tracking, malware risks from compromised[…]

Personalize Your Emails to Boost Engagement and Results
Email marketing is essential for promoting personal brands. Key strategies include building a targeted email list, crafting compelling subject lines, personalizing emails, providing valuable content,[…]

Enhance User Experience with Animation in Design
Incorporating animation into design offers numerous advantages, including increased user engagement, guidance through interactions, enhanced storytelling, and valuable feedback. Animations can effectively attract attention and[…]

The Pros and Cons of Using Popups on Your Website
Will Your Site Use Popups? Popups can be a double-edged sword when it comes to website user experience. Here are some considerations for using them[…]

Effective Email Marketing Strategies for Personal Branding
Email marketing is an effective way to promote your personal brand. Key strategies include building a targeted email list by identifying your audience and creating[…]
Wi-Fi Challenges: Range, Interference, and Security Risks
Wi-Fi technology has several notable limitations. Its range is typically confined to 30 to 100 feet indoors, decreasing further outdoors due to obstacles. Interference from[…]

Key Aspects of Building a Successful Website
When creating a website, define its purpose, target audience, and goals. Choose a memorable domain and reliable hosting. Focus on user-friendly design and quality content.[…]

Top 5 Best FTP Programs for Easy File Transfers
A good FTP program for sending files to your website includes: Choose the one that best fits your operating system and specific needs. Host your[…]

Essential Requirements for Website Features
To ensure effective functionality of your website features, consider several key factors: Firstly, verify that your hosting provider supports the required PHP version and extensions.[…]

Essential Data Privacy Practices for Website Management
When managing a website, it is crucial to consider the types of data collected from visitors, particularly sensitive information such as Personal Identifiable Information (PII),[…]
How to Build a Reliable Small Office Network
To create an effective small office network, essential components include a reliable router with strong security features, a network switch for additional ports, Ethernet cables[…]

Essential Backup Strategies to Minimize Downtime
To minimize system downtime, it’s essential to implement effective backup and recovery strategies. Regular backups should include full, incremental, and differential types. Choose appropriate storage[…]